An Online security agency has reported a new malware called ‘Vega Stealer’ that targets Marketing/Advertising/Public Relations & Retail/Manufacturing industries & tries to steal the saved credentials & credit cards in the Chrome & Firefox browsers, as well as stealing sensitive documents from infected computers. Vega, said ‘proofpoint’ is a variant of August Stealer with only a subset of its functionality as well as several important new features.
On May 8, 2018, proofpoint observed & blocked a low-volume email campaign with subjects such as “Online store developer required.” While some emails were sent to individuals, others were sent to distribution lists including “info@”, “clientservice@”, and “publicaffairs@” at the targeted domains, an approach that has the effect of amplifying the number of potential victims. The messages contained a malicious attachment called “brief.doc” bearing macros that downloaded the Vega Stealer payload.
This campaign was also notable for its targeting. Messages were sent to a narrow set of companies in the Marketing/Advertising/Public Relations and Retail/Manufacturing industries.
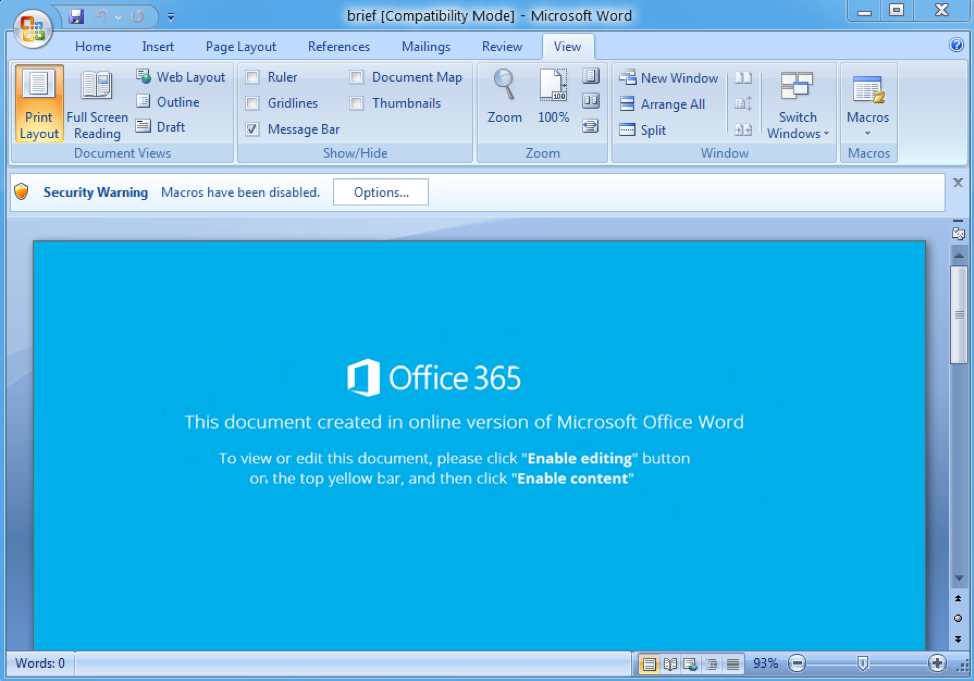
Figure 1: Document attachment containing macros that, when enabled, download Vega Stealer
When the Firefox browser is in use, the malware harvests specific files — “key3.db” “key4.db”, “logins.json”, and “cookies.sqlite” — which store various passwords and keys.
However, Vega Stealer does not wrap up there. The malware also takes a screenshot of the infected machine & scans for any files on the system ending in .doc, .docx, .txt, .rtf, .xls, .xlsx, or .pdf for exfiltration.
Image Credit: proofpoint